Find out what isspying on you
Search for problematic browser extensions across your fleet.
Read the code, not the manifest
We find problems no one else does because we don't just have a static scanner which looks for known patterns.
We read what the code actually does, every line.
This is how:

Deobfuscation
Stylish hid behind 4 layers of base64 + AES-256-CBC + a columnar transposition cipher.
We unwrapped all of it.
Re-analysed on every update
Cyberhaven's attackers didn't change permissions, they changed code. We rescan every release, so a trusted extension can't quietly pivot into a stealer.
Novel-attack detection
LLM pipeline catches what no signature has seen: encoded payloads assembled at runtime, weird egress, page leaks.
Instrumented sandbox
An agent drives the extension like a real user, with aged accounts to trigger gated behavior.
Network egress capture
Every outbound request, traced live
We don't miss the 1 in 1000 that will cause you major problems.

Layered defence. Every finding survives cross-examination before it ever reaches you.
Recently flagged by us
Recent findings.
Works with
every popular browser
The pipeline
From every store to a claim you can audit.
Chrome Web Store
315K extensions
Edge Add-ons
30K extensions
Safari Extensions
12K extensions
Static Analysis
Agents read the bundle before it ever runs. Manifest, code and supply chain.
manifest.json · host_permissions · code-bundle · npm-tree · signing-cert
Dynamic Analysis
Detonated in a sandboxed browser. Every call, request and write is traced.
network.trace · dom.access · storage.io · eval.calls · exfil.detect
Agentic Verification
An agent jury reconciles findings into a single claim with cited evidence.
cross-ref · dedupe · evidence-link · severity-score
Exfiltrates all URLs in real time
8M Users
Trusts main world in cryptographic operations
2M Users
Scoped to single host, no telemetry
700k Users
Latest research.
Deep-dives on the extensions, vendors, and attack patterns our pipeline surfaced.

The Word 'Toad' Gave Any Website Full Control of Chrome's Most Popular VPN
Urban VPN's Chrome extension accepted commands from any website via postMessage with no origin validation. Any page could disconnect your VPN, reroute your traffic, disable security features, and more - silently, with zero user interaction.

Anatomy of a Malicious Extension
Why Permission Scoring Fails
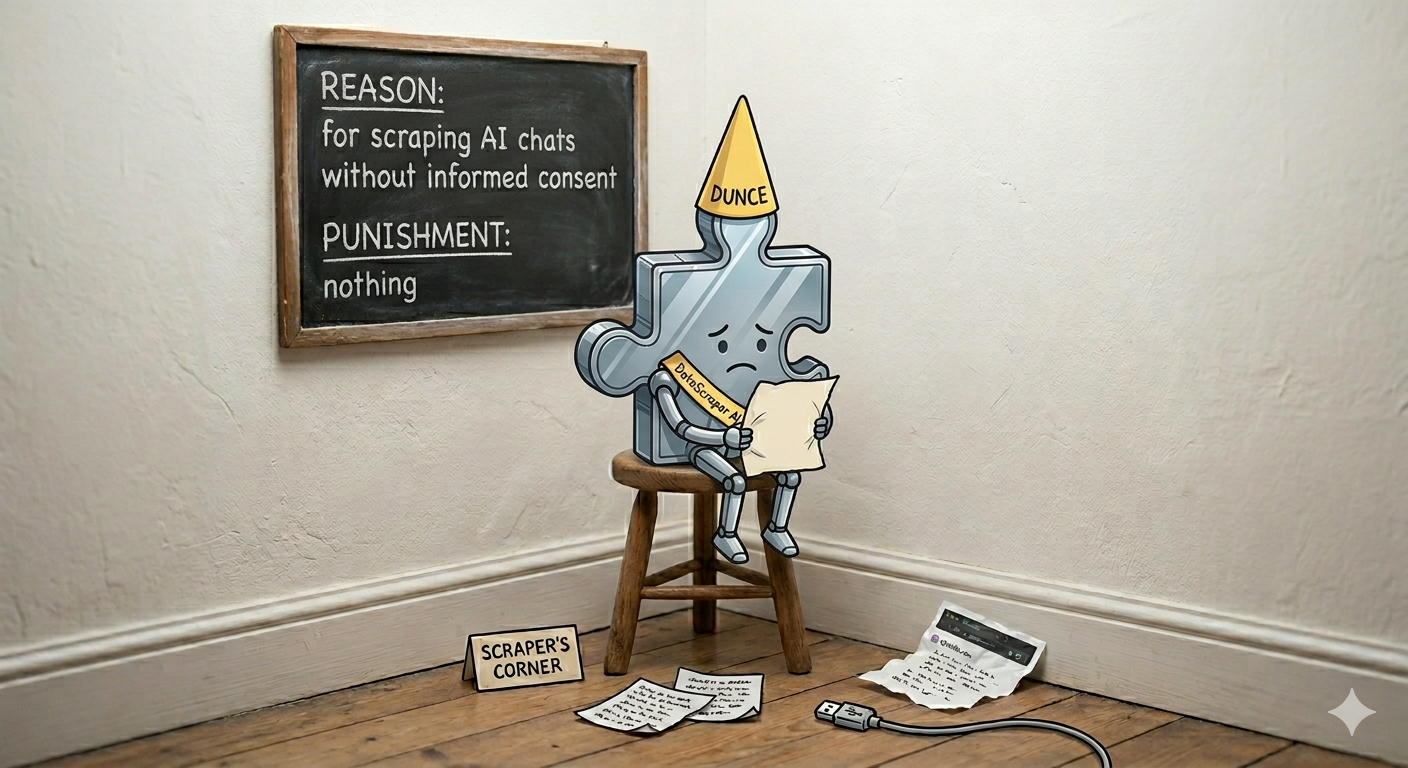
The AI Chat Scraping Extension Wall of Shame

CRXcavator Alternative: Here's how it worked and what we built to replace it.
Join the conversation.
Researchers, security teams, banks, government agencies we've quietly saved from a very bad week.

Nang
CTO, Streamable
At Streamable, we can't afford security incidents and Am I Being Pwned found problematic extensions we had installed.
Centre for Cybersecurity Belgium
Wall of Fame 2026
Recognised for the responsible disclosure of critical vulnerabilities affecting users in Belgium and across the EU.

@phia
Phoebe Gates & Sophia Kianni
Am I Being Pwned made Phia more secure.
Integrations
Plug into your fleet.
Three ways to wire up Am I Being Pwned. Use one or all of them.